I haven't done much research on the company itself, but a Google search for "conduit toolbar" will show you just how many people search for this crapware, and how many people have created a "how-to" in order to uninstall the application. The company (Conduit) has a very plain page without offering much detail and appears to be affiliated with a company called Como, which helps businesses create smart phone apps. Whatever, I don't care. I just want the network indicators.
The main reason why I created this post was to, obviously, show you some network indicators for this toolbar. I had a hard time finding any kind of information about indicators for the toolbar; almost all of the sites that I found had information on how to uninstall the toolbar. What does the toolbar do? Well it is pretty malicious and transmits sensitive data to a remote server. File analysis shows that it will attempt to see if a virtual machine is running (anti-forensics), will steal private information from your web browser, fingerprint your system (BIOS, MachineGUID), and even modify your proxy settings. Yeah, this is a nice piece of software. On to the network indicators!
Domains Contacted / HTTP URI Paths:
The following domains are contacted after installation and for application updates. The HTTP URI paths below each domain have been observed for those specific domains.
- sp-storage.conduit-services.com
- /autoupdate/
- sp-storage.spccinta.com
- /autoupdate/
- sp-storage.spccint.com
- /autoupdate/
- servicemap.conduit-services.com
- /sp/
- /sptray/
- servicemap.spccint.com
- /sp/
- /sptray/
- sp.api.search.conduit.com
- /up/settings/?ctid=
- sp-alive-msg.conduit-data.com
- sp-alive-msg.databssint.com
- sp-autoupdate.conduit-services.com
- /autoupdate/
- /update/
- sp-autoupdate.spccint.com
- /autoupdate/
- /update/
- sp-ip2location.conduit-services.com
- /ip/?client=sp
- sp-ip2location.spccint.com
- /ip/?client=sp
- sp-settings.conduit-services.com
- /searchprotectorsettings/
- /carrier/
- /plugins/
- sp-settings.spccint.com
- /searchprotectorsettings/
- /carrier/
- /plugins/
- sp-translation.conduit-services.com
- /?locale=
- sp-usage.databssint.com
HTTP User-agent String:
- Starts with: "SearchProtect"
- Users a semi-colon as a field separator
- Breakdown of user-agent string values:
- SearchProtect;<Application Version>;<OS type and version>;<Unique identifier>
- Example:
- SearchProtect;1.7.1.50;Microsoft Windows 7 Professional;SP1A9B0A2A-43A1-4D4B-C21B-4CAEDF6B9192
- Regex to find the unique identifier on the user-agent string:
- ([a-zA-Z0-9]{10}\-[a-zA-Z0-9]{4}\-[a-zA-Z0-9]{4}\-[a-zA-Z0-9]{4}\-[a-zA-Z0-9]{12})
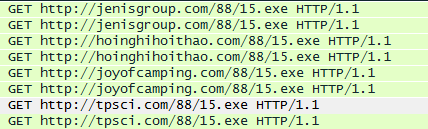
File Downloaded:
An associated file that is downloaded for updating is retrived from the following sites:
- sp-storage.conduit-services.com
- sp-storage.spccinta.com
- sp-storage.spccint.com
Download activity is accomplished thorugh an HTTP GET request over port 80 for the file name "autoupdate.zip."
Further Reading:
- autoupdate.zip file analysis:
- https://www.virustotal.com/en/file/f78da944c348e7f9df99c1c9073f47b25c95f9d44567c6c48d3ab4746237b03b/analysis/
- https://malwr.com/analysis/MjBmZjYwZDg2ZmNjNDJlYzgyZWU1NmQ3YmQwYTViMTc/
- https://www.hybrid-analysis.com/sample/49ef551698fe7b2530991d5436b54284f722ab5e4ea951802677c3a6a8e5489b?environmentId=5